TM Streamyx Router Wi-Fi Security
If you are using the router that came with your telco provider, please take immediate action to verify its security settings, in particular Wi-Fi.
Last week while at someone else’s house, I discovered that default settings of the router provided by telco had not one but 4 Wi-Fi SSIDs. One of them was already secured with a long WPA2 password, good. However, the remaining 3 were without security. Their SSIDs were hidden but hiding SSID is not a form of security!
Motivation
Streamyx is an ADSL internet service provided by TM, a telco provider in Malaysia. I do not use TM Streamyx anymore.
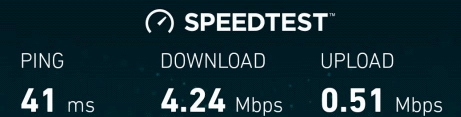
Last week, I stayed over at a house that was using Streamyx. The speed of the owner’s subscription was 4Mbps which is decent but given that I have used 512Kbps and 1Mbps of Streamyx in the past, I could not help but notice the 4Mbps was lagging in latency and low in throughput.
Multiple speed tests confirmed it, achieving just a little over 2Mbps.
So what could be wrong, I asked myself.
Wi-Fi router security checks
Wireless security
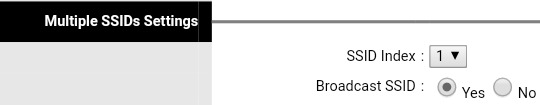
This was the first and actually the only area I looked at because I found very glaring security holes. I inspected the Wireless security setup and found that it supports multiple SSIDs, 4 to be exact.
Hidden SSIDs without security
Index 1 has been set to broadcast SSID, WPA2-PSK authentication type with long AES encryption key. This is fine until I flipped the SSID index to 2, 3 and 4 where I discovered they were set to require no authentication! The SSIDs were Riger1, Riger2, and Riger3.
It is fine to keep SSID hidden if you do not want to connect to it at all. Otherwise, I do not recommend hiding due to a fundamental drawback; your devices would need to be set to connect to hidden SSIDs manually or if you leave it in auto, it will be attempt to connect non-stop, draining your battery as a result.
Security through obscurity
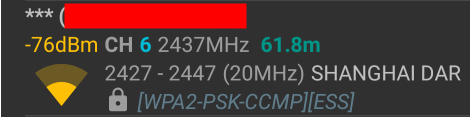
Security through obscurity is no security. Using commonly available Wi-Fi channel detection app on Android, it possible to discover the presence of hidden Wi-Fi with names masked.
If you want to know how to uncover hidden SSIDs, you can Google for it. It is beyond the scope of this post.
I verifed that Riger1 is indeed open and usable, Likewise the other two.
There are others who have recommended changing the default SSIDs to something more obscure but this is in itself not a form a security. Secondly, restricting access to specified MAC addresses serves to inconvenient router administrators, by that I mean you. MAC addresses can be spoofed so do not even bother with this option.
Real security
Real security is achieved through use of common security standards that are not been considered broken, i.e. using WPA2-PSK authentication and AES encryption with super long key. Apply that to the 3 Riger SSIDs. Also, please change the SSIDs to something random so that your router does not receive needless connection attempts from potential Wi-Fi freeloaders.
Thereafter, a round of speed test to appreciate its true speed.